Modern Cyberattacks: India’s new-age battlefield and the road to resilience

By Saiprasad Iyer, Techsec Digital The Silent Backbone of Modern Manufacturing & Healthcare Industry Operational Technology (OT) systems form the beating heart of critical industries — from manufacturing and energy to transportation and utilities. These systems control physical processes, monitor industrial operations, and keep factories, power grids, and pipelines running. Yet, as industries embrace digital […]
Understanding The Digital Personal Data Protection (DPDP) act & its Solution.
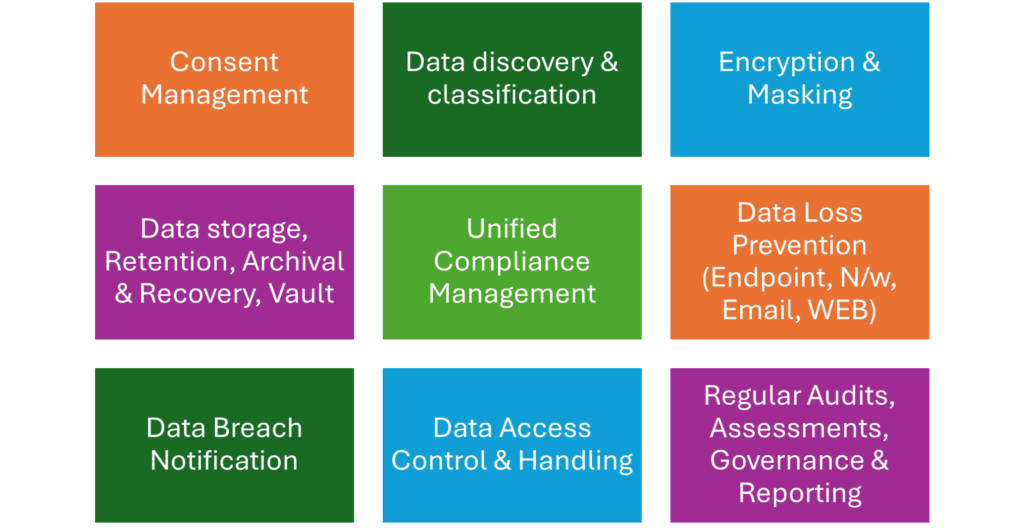
The Digital Personal Data Protection (DPDP) Act is India’s law to protect digital personal data, enacted in 2023 is yet to take effect, which aims to give individuals more control over their data and hold companies accountable for how they process it. Businesses must comply with its rules for collecting, storing, and processing personal data, with consequences including […]
Use-Cases of CVEM: Continuous Vulnerability & Exposure Management.

Continuous Vulnerability and Exposure Management (CVEM) is a proactive security approach that goes beyond traditional vulnerability scanning to continuously identify, prioritize, and remediate all security weaknesses. Instead of focusing only on known CVEs, CVEM considers the full scope of risks, including software vulnerabilities, misconfigurations, and security control anomalies. Use cases of continuous vulnerability and exposure […]
Securing the Unseen: The Rising Need for OT Security in a Hyperconnected World

By Saiprasad Iyer, Techsec Digital The Silent Backbone of Modern Manufacturing & Healthcare Industry Operational Technology (OT) systems form the beating heart of critical industries — from manufacturing and energy to transportation and utilities. These systems control physical processes, monitor industrial operations, and keep factories, power grids, and pipelines running. Yet, as industries embrace digital […]
Securing the Cloud-Native Future: How CNAPP Redefines Cloud Security for Modern Enterprises

Securing the Cloud CNAPP As organizations have accelerated their cloud transformation beyond the traditional boundaries of IT infrastructure. Applications are now distributed, dynamic, and built using containers, Kubernetes, microservices, and serverless functions. While these advancements drive agility and scalability, they also introduce complex security challenges. This is where Cloud-Native Application Protection Platforms (CNAPP) come in […]
CIO Convergence

CIO Convergence 2025 Panel Spotlight | CIO Convergence 2025 Hosted by M/s. International Business Intelligence Panel Discussion: “IT Cost Optimization – Doing More with Less” In an era of tightening budgets, CIOs face the challenge of driving innovation without overspending. This insightful session at CIO Convergence 2025 explored how organizations can optimize IT costs through […]
Security Circle Mumbai 2025

Security Circle Mumbai 2025 A Bold Step Into Cybersecurity Conversations Security Circle Mumbai 2025 was not just an event—it was Techsec Digital Global Private Limited first bold step into the world of cybersecurity conversations, and what a powerful start it was. As our debut event, it was incredibly special to witness such an inspiring convergence of visionaries […]
Modern Data Loss Prevention: Safeguarding Enterprise Data in 2025

Modern Data Loss Prevention: Safeguarding Enterprise Data in 2025 Modern Data Loss Prevention: Safeguarding Enterprise Data in 2025 Corrected Blog : 20/10/2025 The High Cost of Data Loss and Why DLP is Essential Data is the lifeblood of modern enterprises – and losing control of that data can be devastating. Whether through a cyber breach […]
How AI – powered SIEM Transforms Enterprise Security

How AI-Powered SIEM Transforms Enterprise Security How AI-Powered SIEM Transforms Enterprise Security Corrected Blog : 20/10/2025 Security Operations Center (SOC) teams today face an overwhelming deluge of alerts and data. Studies show 71% of SOC analysts report burnout from alert overload, with 62% of security alerts getting ignored entirely due to sheer volume. Traditional SIEM (Security […]

