
Corrected Blog : 20/10/2025
Data is the lifeblood of modern enterprises – and losing control of that data can be devastating. Whether through a cyber breach or accidental exposure, data loss incidents cost companies dearly. The average cost of a data breach reached $4.88 million in 2024, according to IBM “Cost of data breach report’. Beyond direct financial impact, organizations face regulatory fines, reputational damage, and loss of customer trust. Regulations such as GDPR, HIPAA, PCI DSS mandate strict data protection, with severe penalties for non-compliance. In its 2024 DLP market quadrant report, The Radicati Group projects the DLP market to grow from $2.7 billion in 2024 to over $7 billion by 2028. Markets and Markets similarly projects strong growth, from $3.4 billion in 2023 to $8.9 billion by 2028.
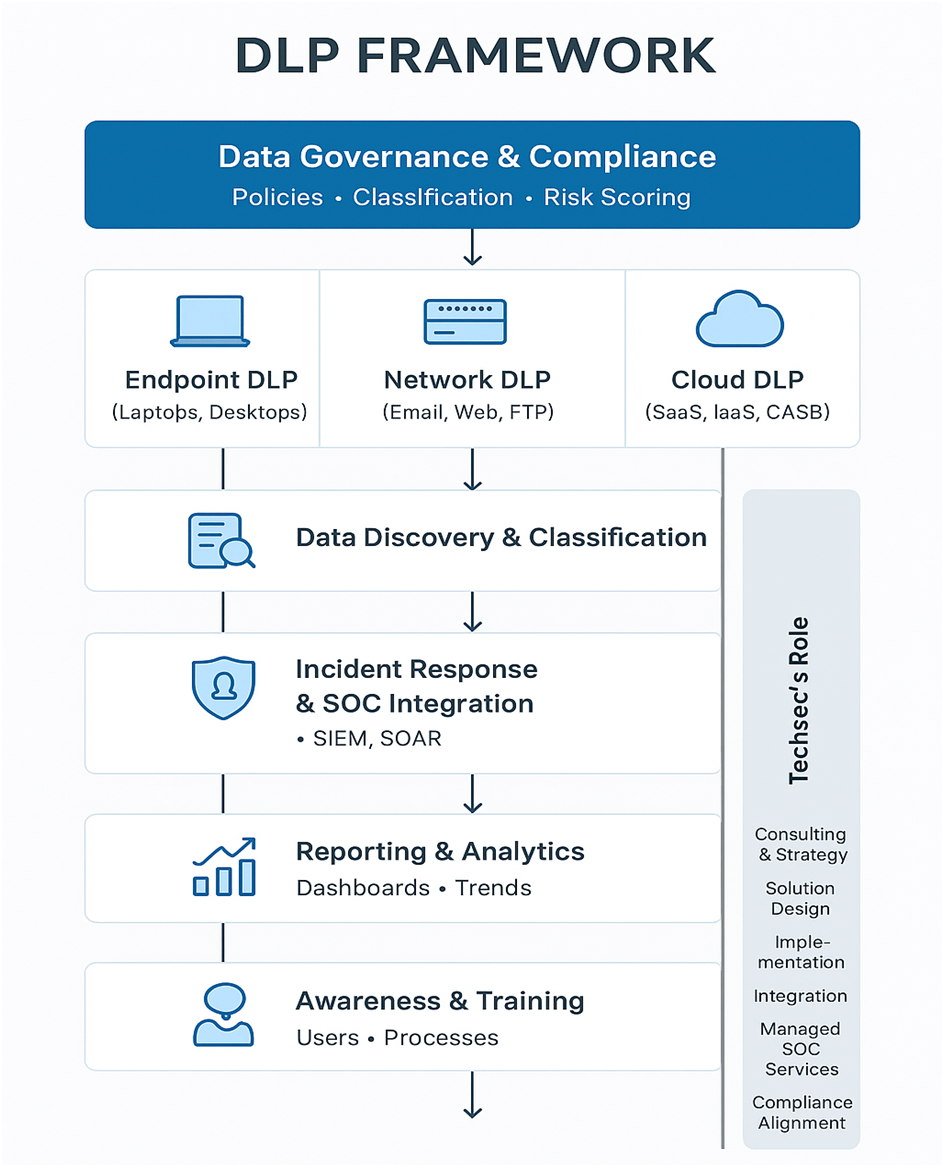
A strong DLP program protects data at rest, in use, and in motion by covering all major fronts:
A unified approach across endpoints, networks, and cloud ensures that whether data resides on a laptop, is being emailed, or is in a cloud app, it remains protected.
While cybercriminals make headlines, insiders — often unintentionally — are behind most data loss incidents. Simple mistakes like sending an email to the wrong recipient or saving a file to an unapproved location can expose sensitive data.
Key steps to deploy DLP successfully:
Implementing DLP can be complex — but Techsec Digital makes it straightforward. As a trusted system integrator, Techsec works with leading OEM partners to provide end-to-end DLP solutions tailored to your organization’s needs, compliance requirements, and risk profile.
What We deliver:
By partnering with Techsec Digital, enterprises gain not just tools but also the expertise and guidance to deploy them effectively, ensuring that sensitive data stays protected everywhere.
| Layer | Description | Key Technologies / Tools | Techsec’s Role |
| 1. Data Classification & Discovery | Identify & classify sensitive data across endpoints, servers, cloud, and SaaS | Data discovery scanners, content inspection engines, metadata analysis | Conduct data discovery workshops, deploy classification tools, map data flow |
| 2. Policy Definition & Governance | Define “sensitive data” and how it should be handled | DLP policies, regulatory mapping (GDPR, DPDP Act, PCI-DSS) | Develop policies & align with compliance frameworks |
| 3. DLP Enforcement Layer | Apply policies to block, monitor, or encrypt data | Endpoint DLP, Network DLP, Cloud DLP (CASB, M365 Purview DLP, Symantec DLP, Forcepoint) | Deploy, configure, and integrate chosen DLP products |
| 4. Monitoring & Incident Response | Detect and respond to violations | SIEM + SOAR + SOC monitoring | Techsec SOC can integrate DLP logs for 24×7 response |
| 5. Reporting & Analytics | Visualize DLP events and trends | Dashboards, compliance reports | Develop executive dashboards & management reporting |
| 6. Awareness & Training | Minimize human-error-based data leaks | LMS, phishing simulation, training | Conduct user training & change management |
In today’s environment of escalating cyberthreats, remote work, and stringent data privacy laws, Data Loss Prevention is mission-critical for Enterprises & any Organization’s.
A strong, well-implemented DLP strategy:
With Techsec Digital as your Data Security partner, you can safeguard your organization’s most valuable asset — its data — and empower your business to innovate securely.