
By Saiprasad Iyer, Techsec Digital
Operational Technology (OT) systems form the beating heart of critical industries — from manufacturing and energy to transportation and utilities. These systems control physical processes, monitor industrial operations, and keep factories, power grids, and pipelines running. Yet, as industries embrace digital transformation, this once-isolated world of OT is now deeply intertwined with IT networks, creating new possibilities — and unprecedented vulnerabilities.
Cyber attackers no longer target only corporate data centers or cloud applications. They now aim for the very systems that drive production and infrastructure. The recent attacks in all the above-mentioned industry have proven how a breach in OT environments can lead to large-scale disruption, safety hazards, and financial loss.
The convergence of IT and OT means that legacy control systems — designed for reliability, not cybersecurity — are now exposed to internet-connected threats. Attackers exploit insecure protocols, unpatched devices, or misconfigured gateways to move laterally from IT to OT networks, often going undetected for months.
Many organizations still treat OT security as an afterthought. The common misconceptions include:
This mindset leaves OT systems operating in the dark — invisible to traditional security monitoring and incident response teams.
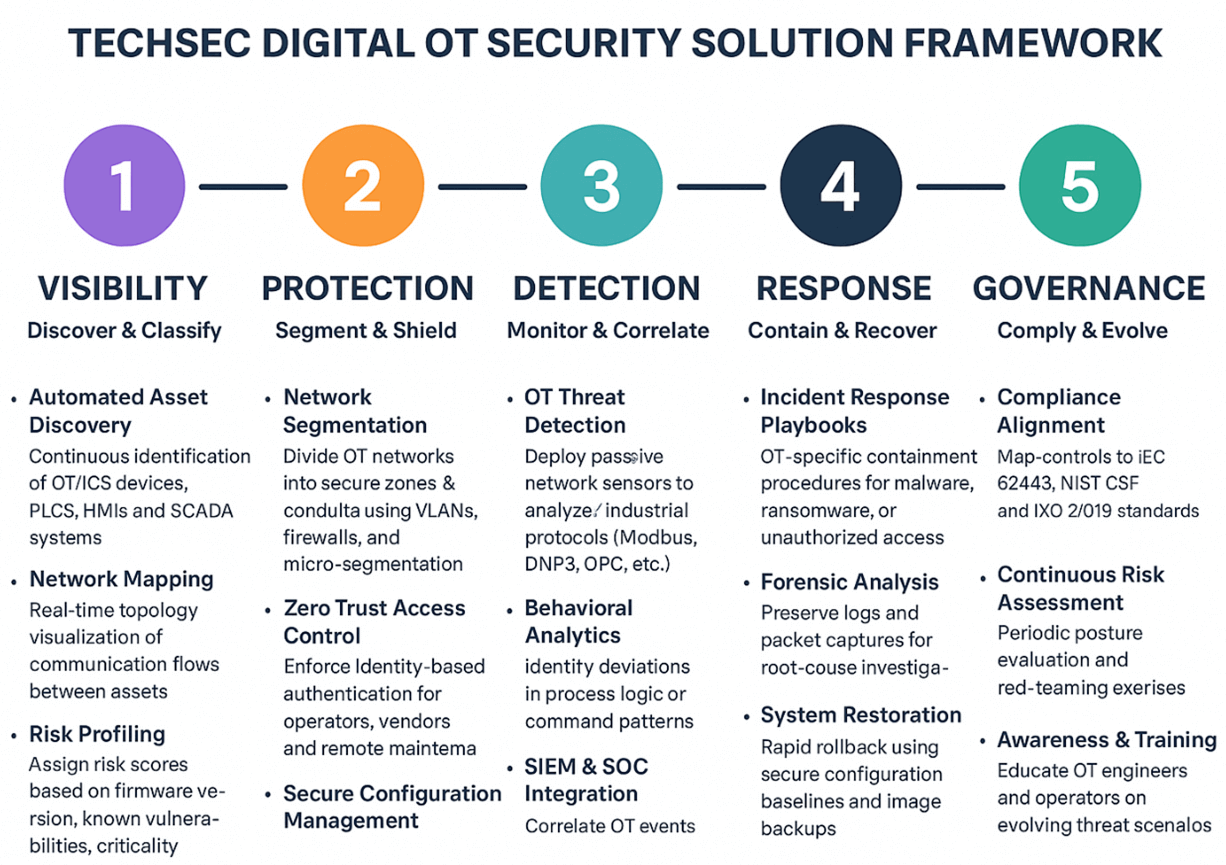
A modern OT security strategy must combine visibility, control, and intelligence.
At Techsec Digital, we advocate a layered approach:
As industries accelerate toward smart manufacturing, digital twins, and industrial IoT, OT security can no longer lag. It must evolve into a proactive, data-driven discipline integrated with enterprise cybersecurity strategy.
The goal is clear — to ensure operational continuity without compromising safety or trust.