Continuous Vulnerability and Exposure Management (CVEM) is a proactive security approach that goes beyond traditional vulnerability scanning to continuously identify, prioritize, and remediate all security weaknesses. Instead of focusing only on known CVEs, CVEM considers the full scope of risks, including software vulnerabilities, misconfigurations, and security control anomalies.
Use cases of continuous vulnerability and exposure management
- Asset visibility and management: To protect against threats, organizations must first know what assets they have. CVEM provides continuous and complete visibility over all IT assets, from on-premises infrastructure to cloud environments, ensuring all devices are accounted for and monitored.
- Integrated vulnerability assessment and remediation: CVEM uses automation to unify and streamline the entire vulnerability management lifecycle, including assessment and remediation, from a single, centralized console. This eliminates reliance on multiple, disconnected tools.
- Patch Management: Patch management is the process of regularly identifying, acquiring, testing, and deploying updates (“patches”) for software, operating systems, and firmware to fix security vulnerabilities, correct bugs, improve performance, and add new features. It is a critical cybersecurity practice to protect systems from threats and maintain their stability and functionality. This process is a continuous cycle that can be automated to reduce human error and save time.
- System configuration hardening: CVEM helps proactively defend against cyberattacks by continuously detecting and fixing misconfigurations and security anomalies. This hardens system configurations and significantly reduces the attack surface.
- Enhanced risk prioritization: CVEM moves beyond basic severity scores (like CVSS) to prioritize vulnerabilities based on business context, asset criticality, and active threat intelligence. This allows security teams to focus on the most impactful risks first, optimizing resource allocation.
- Continuous compliance: CVEM automates the monitoring and enforcement of compliance policies by continuously scanning and fixing compliance issues in real-time. This helps organizations maintain a continuous, audit-ready compliance posture.
- Improved cyber resilience: By integrating and automating all stages of vulnerability management, CVEM strengthens an organization’s overall defence. This increases resilience and helps prevent vulnerabilities from being exploited in the first place.
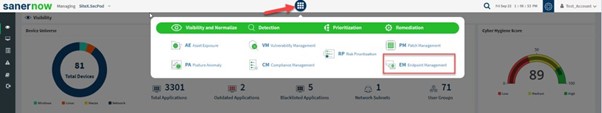
- Endpoint Management: This module under CVEM is a cloud-based service that offers comprehensive visibility and control over all endpoints within a network. It simplifies day-to-day administrative and security tasks by using a lightweight, multi-functional agent that works on various operating systems, including Windows, macOS, Linux, and AIX. The key features are Centralised Software deployment, comprehensive visibility, application & device control, remote access, remote scripting & many more.
- Cloud security: CVEM offers continuous assessment and remediation capabilities specifically for cloud-based environments. As organizations shift more workloads to the cloud, CVEM helps security teams manage the unique challenges of cloud infrastructure.
- Audit-ready reporting: Because it provides a consolidated, real-time overview of an organization’s security, CVEM can generate actionable, customizable reports that are ready for compliance audits.

How Techsec Digital can help
Techsec Digital uses a holistic approach and cutting-edge technology, including platforms like SecPod Saner, to deliver comprehensive CVEM services. Their offerings enable organizations to gain control of their exposure management.
What we can offer
• The Solution & Product (re-sale)
• Strategic consulting
• Managed Security Services
• Professional Services & Deployment
• Monitoring and Remediation
• Vulnerability & Penetration Testing
Prevent Tomorrow’s Attacks, today by deploying a Unified and All in One Security Platform.